Controlling group access to CLC Server data
Folders are the basic unit for controlling access to data. Permissions applied to a folder also apply to the data elements within it. This section describes how to control access to folders in CLC Server File System Location where permissions have been enabled and the "Group-based permissions" option has been selected.
When group-based permissions are first enabled on a CLC Server File System Location, only the root user or users in the admin group will have access to data stored there. Permissions can then be granted on folders. can then be granted on folders to specified groups by administrators logged into the web client or logged into a CLC Workbench acting as a client for the CLC Server.
Members of groups can be granted two types of access:
- Read access
- Elements in these folders can be listed, opened or copied using the CLC Server Command Line Tools, the web client, or a CLC Workbench, for example by browsing in the Navigation Area, searching, or clicking the "Originates from" link in the History (
 ) of a data element.
) of a data element.
- Write access
- New elements and subfolders can be created in this area, and changes made to existing data or folders can be saved.
Note: To access a folder and its contents, a user must be a member of a group with read access to all the folders above it in the hierarchy. In the example shown in figure 6.1, to access the Sequences folder, the group must have access to both the Example Data and Protein folders.
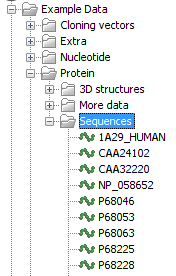
Figure 6.1: A folder hierarchy as seen through a CLC Workbench Navigation Area.
It is fine to give write access to just the final folder in a hierarchy. For example, in the hierarchy shown in figure 6.1, read access could be granted to the Example Data and Protein folders, with read and write access granted to just the Sequences folder.
Folders that a user has access to are listed at the top of a given CLC location in the Navigation Area of a CLC Workbench when logged into the CLC Server (figure 6.2).
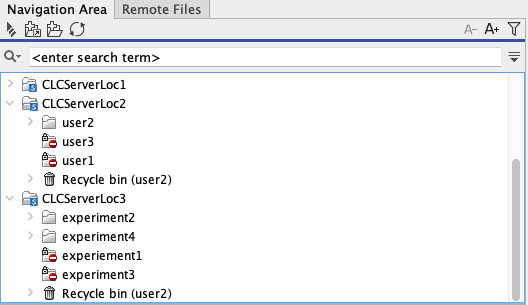
Figure 6.2: A user called "user2" has logged into a CLC Server with 3 locations. Group-based permissions were enabled for the CLCServerLoc3 location and user2 belongs to a group with access to the experiment2 and experiment4 folders. Thus these are listed at the top of that location in the Workbench Navigation Area. The CLCServerLoc2 location was configured with the "User homes" option, so the user2 folder, accessible by this user, is listed at the top of that location.
Please see Technical notes about permissions and security for further details about the system behavior relating to permissions.
Subsections
