LDAP directory
This option will allow you to use an existing LDAP directory. Information needed during authentication and group memberships is then retrieved from that LDAP directory (figure 4.3).
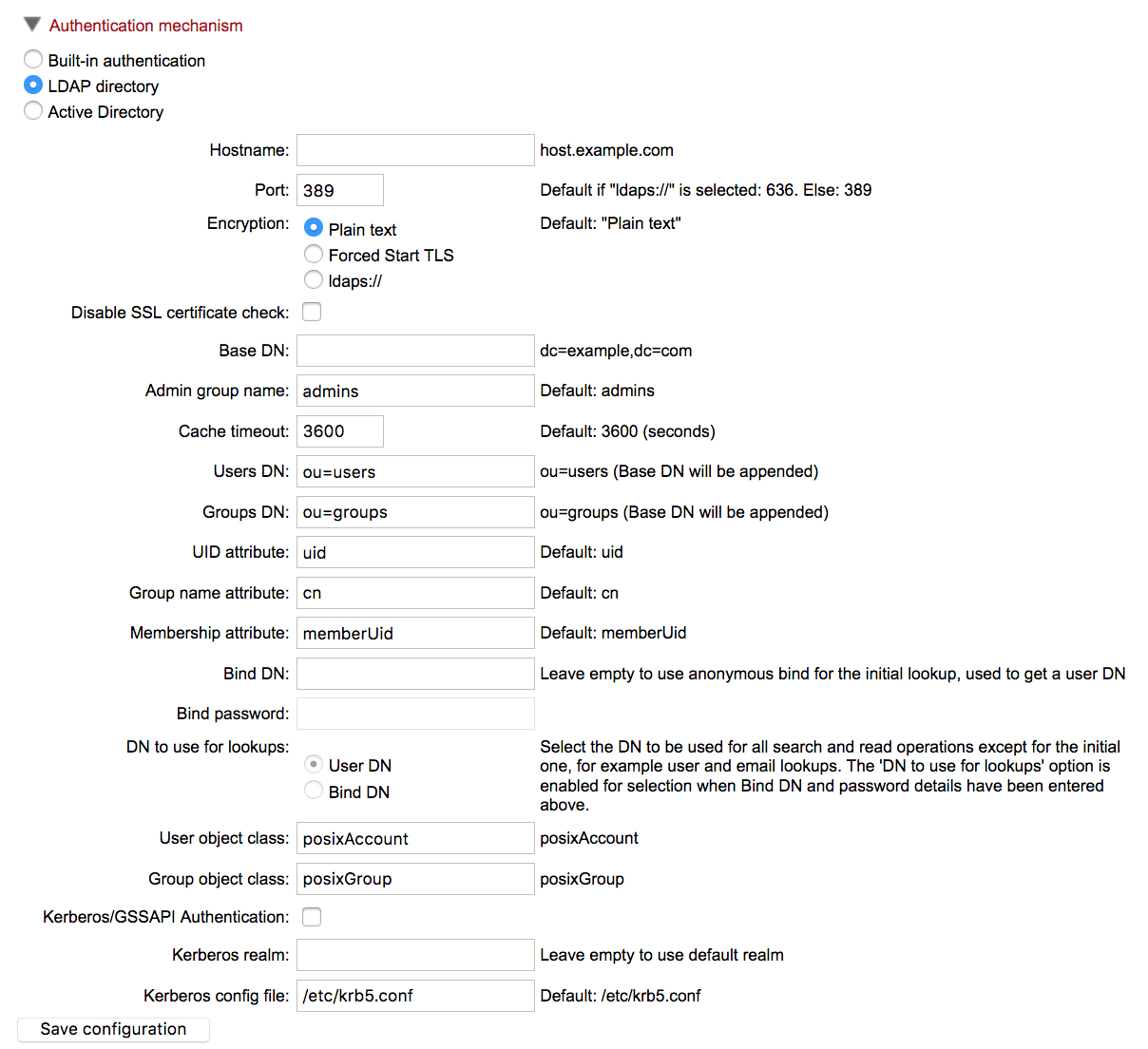
Figure 4.3: LDAP settings panel.
Configuration option information
Kerberos/GSSAPI Authentication Enable the LDAP integration to use Kerberos/GSSAPI.
Encryption The default is Plain text, with options available for encryption using Start TLS ("Forced Start TLS") or LDAP over SSL ("ldaps://").
DN to use for lookups This allows you to choose which bind should be used for read and search operations. If no bind DN have been entered an unauthenticated bind will be used to do the initial lookup (lookup of users DN based on the username), and all other read and search operations will be performed with users binds. If the Bind DN and Bind password have been filled in, you have the choice between using the 'Bind DN' or the 'User DN' for read and search operations, the 'Bind DN' will in this case always be used for the initial lookup.
User object class and Group object class Intended for use where the standard posixAccount and posixGroup classes are not appropriate.
Certificates
If your LDAP server uses a certificate that is not generally trusted by the server system that the CLC Server software is running on, then it must be added to the truststore of the CLC Server installation (CLC_SERVER_BASE/jre/lib/security/cacerts, where CLC_SERVER_BASE is the server installations root location). This can be done with the keytool shipped with Java installations (also available in the CLC_SERVER_BASE/jre/bin/keytool), with a command like:
CLC_SERVER_BASE/jre/bin/keytool -import -alias \ ldap_certificate -file LDAP_CERTIFICATE.cer -keystore \ CLC_SERVER_BASE/jre/lib/security/cacerts -storepass changeitReplace LDAP_CERTIFICATE with the path to the certificate your LDAP server uses for Start TLS/LDAPS connections. Replace CLC_SERVER_BASE with the path to the servers installation location.
For a node setup, this must be done for all job nodes as well.
Caution: If you update the server installation or reinstall the server, all imported certificates will be removed, and have to be imported again. You should also be aware that certificates have an expiration date, and will not be trusted after this date. Make sure to add a new certificate in advance of the expiration date.
